This article introduces the Actor Profile Designer methodology. By quantifying an adversary's proficiency across the 10 TLCTC clusters, organizations can visualize strengths via spider diagrams, identify potential attack paths, and export profiles as PDF Actor Cards or JSON for strategic risk integration.
Tool Overview
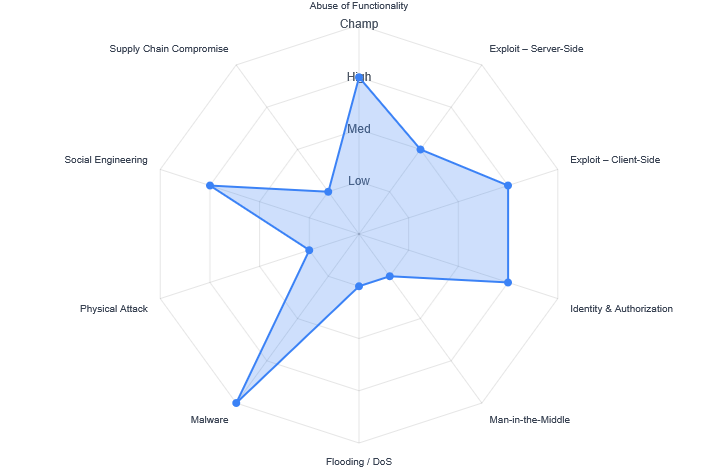
The Actor Profile Designer quantifies an adversary's proficiency across the 10 TLCTC clusters, visualizing their strengths and potential attack paths. The tool utilizes a Spider (Radar) Diagram to provide an instant visual fingerprint of the actor's capabilities.
Scoring Capabilities
To ensure consistency in threat profiling, we utilize a standardized 4-point scale mapped to the technical proficiency required for each Cluster. In the radar diagram, the center represents 0 (No Capability) and the outer boundary represents 4 (Champion).
- 1 = Low: Script Kiddie / Basic Tool Use
- 2 = Medium: Competent / Modified Tools
- 3 = High: Proficient / Zero-Day Discovery
- 4 = Champion: State-of-the-Art / Supply Chain Mastery
Understanding Metrics
Beyond simple scores, the Profile Designer calculates derived metrics to help strategic decision-making:
- Max Score: The highest capability exhibited by the actor (Outer Boundary).
- Dominance Index: The gap between the 1st and 2nd best skill, indicating if an actor is a "One Trick Pony" or a versatile threat.
- Breadth: The total count of skills rated High or Champion, indicating the resourcefulness of the group.
Full Dataset: Google APT Groups
We have mapped over 40 distinct Threat Actors from the Google Cloud Security APT Groups insights into the TLCTC JSON format. This dataset serves as a baseline for importing into the Actor Profile Designer app.
CTA-Google-APT-Groups.json
Contains profiles for APT41, APT29, APT28, and more.
{
"schema_version": "tlctc-actor-profile.v1",
"score_scale": "1=Low, 2=Medium, 3=High, 4=Champion",
"source": "https://cloud.google.com/security/resources/insights/apt-groups",
"actors": [
{
"threat_actor": "APT41 (Double Dragon, Winnti)",
"tlctc_scores": { "TLCTC-01.00": 3, "TLCTC-02.00": 2, "TLCTC-03.00": 3, "TLCTC-04.00": 3, "TLCTC-05.00": 1, "TLCTC-06.00": 1, "TLCTC-07.00": 4, "TLCTC-08.00": 1, "TLCTC-09.00": 3, "TLCTC-10.00": 1 },
"notes": "China-nexus... Champion Malware use (46+ families, rootkits, bootkits)..."
},
{
"threat_actor": "APT29 (Cozy Bear, Nobelium)",
"tlctc_scores": { "TLCTC-01.00": 3, "TLCTC-02.00": 1, "TLCTC-03.00": 2, "TLCTC-04.00": 1, "TLCTC-05.00": 1, "TLCTC-06.00": 1, "TLCTC-07.00": 4, "TLCTC-08.00": 1, "TLCTC-09.00": 3, "TLCTC-10.00": 4 },
"notes": "Sophisticated Russian state-sponsored group... Champion Supply Chain compromise [#10]..."
}
]
}* Note: This is a truncated preview. Download the file for the full 40+ actor dataset.
Conclusion
By moving from qualitative descriptions to quantitative spider diagrams, security leaders can better visualize where their defensive gaps align with the capabilities of their most likely adversaries.
References
- Kreinz, B. Top Level Cyber Threat Clusters (TLCTC), White Paper V1.9.1.
- Google Cloud Security, APT Groups Insights.
