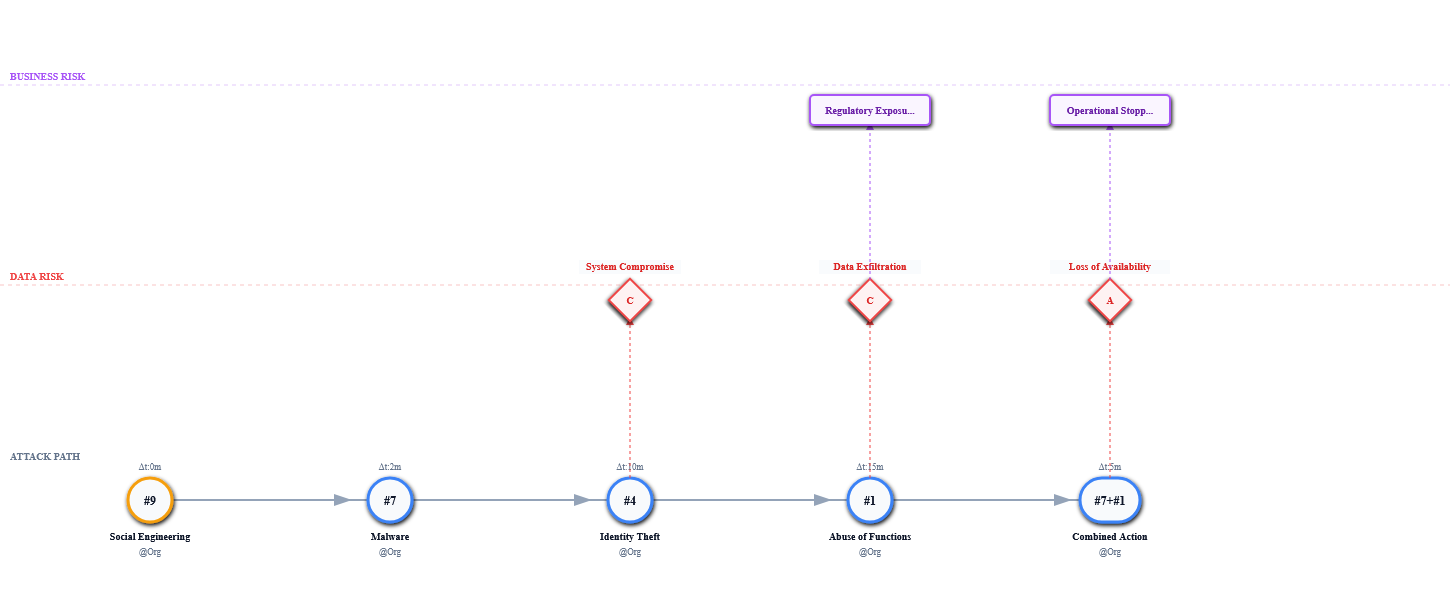
SOC Incident Threat Modeling · v3.0
The official IDE for TLCTC. Model complex attack paths, calculate Attack Velocity (Δt), and export standardized JSON schemas for your SOAR.
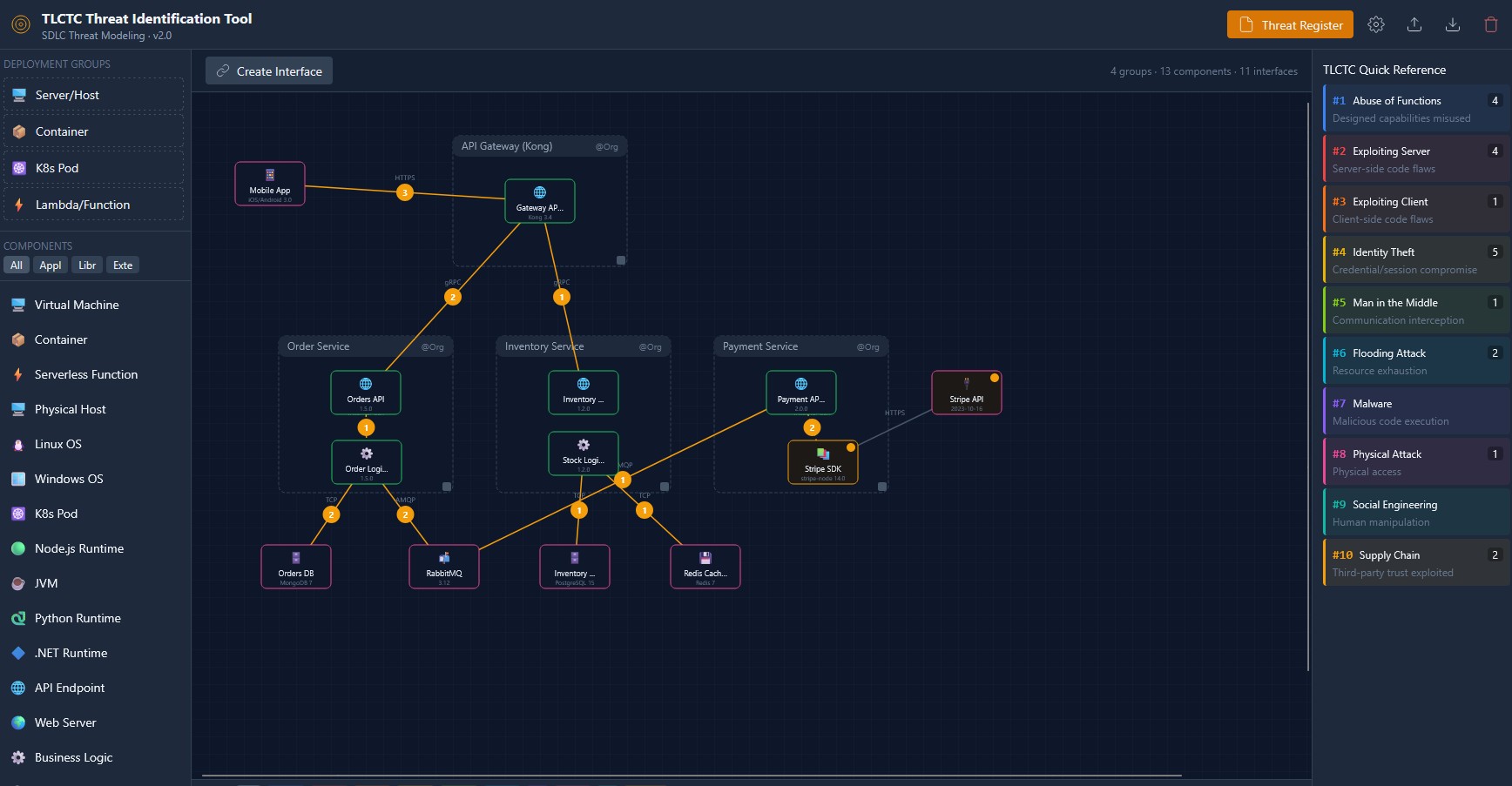
SDLC Threat Modeling · v2.0
The official IDE for TLCTC. Model attack paths, set Attack Velocity (Δt), and export standardized JSON schemas for your threat register.
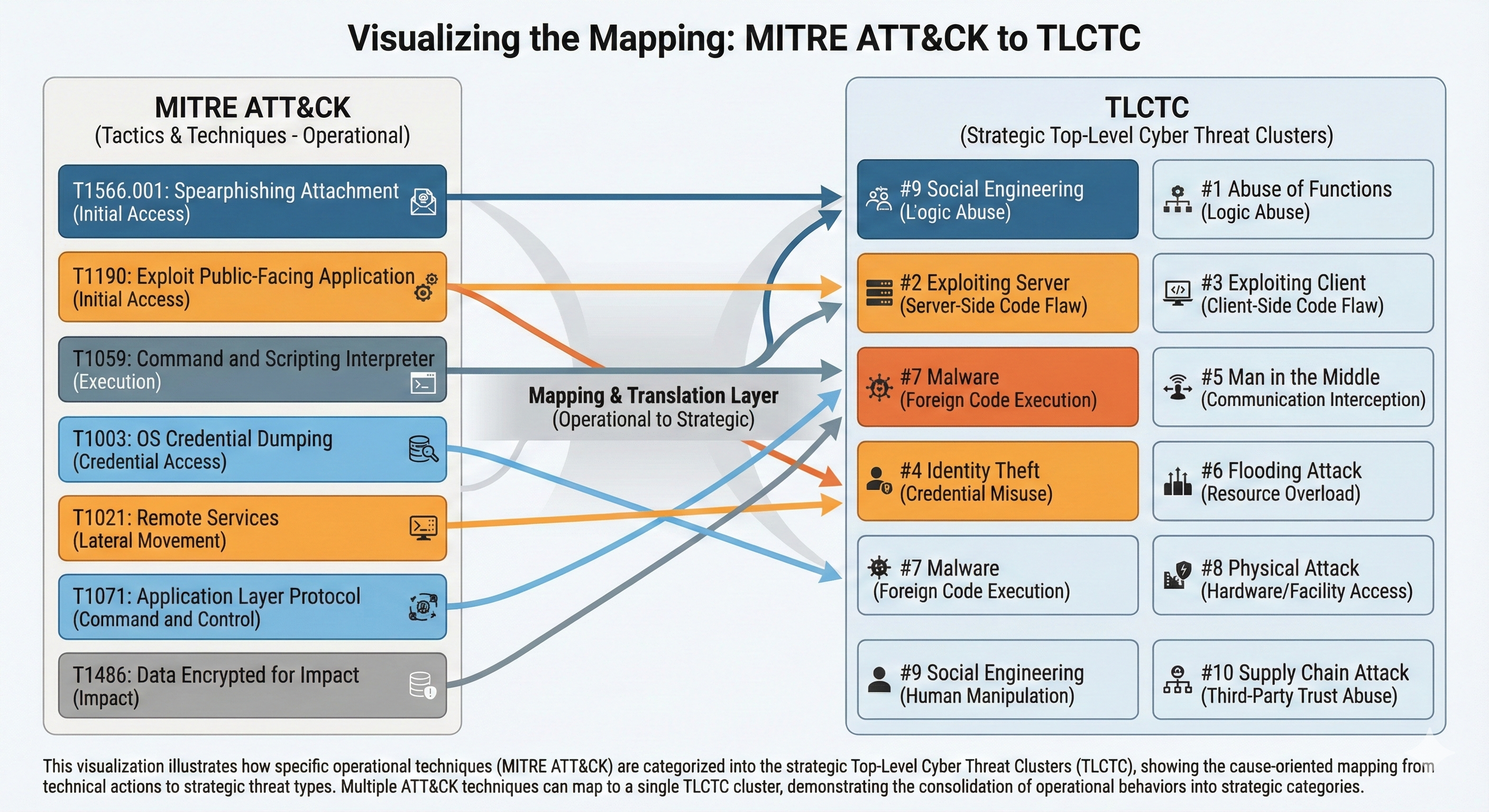
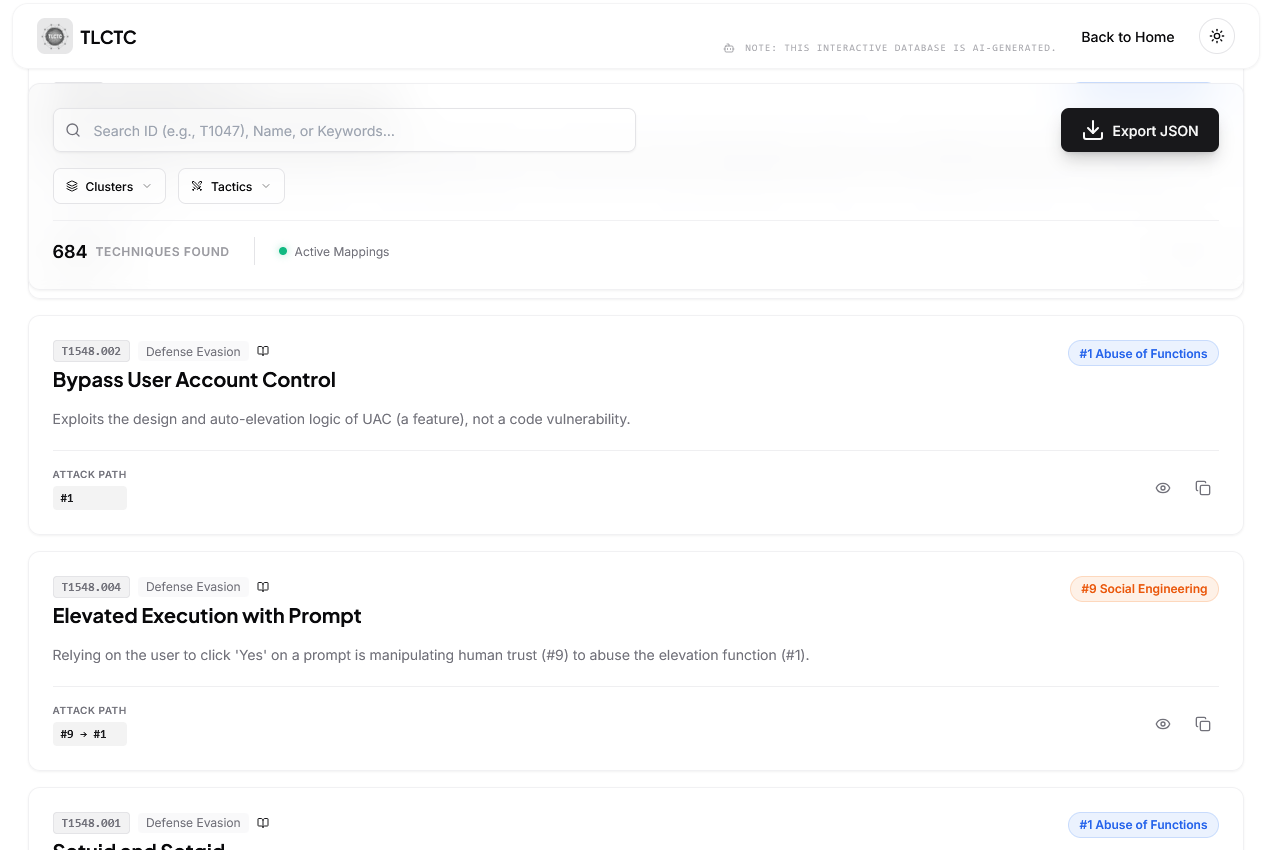
MITRE ATT&CK TLCTC MAPPER
Explore the complete mapping database interactively. Filter by Tactic, Technique, or TLCTC Cluster to see the relationships in real-time.
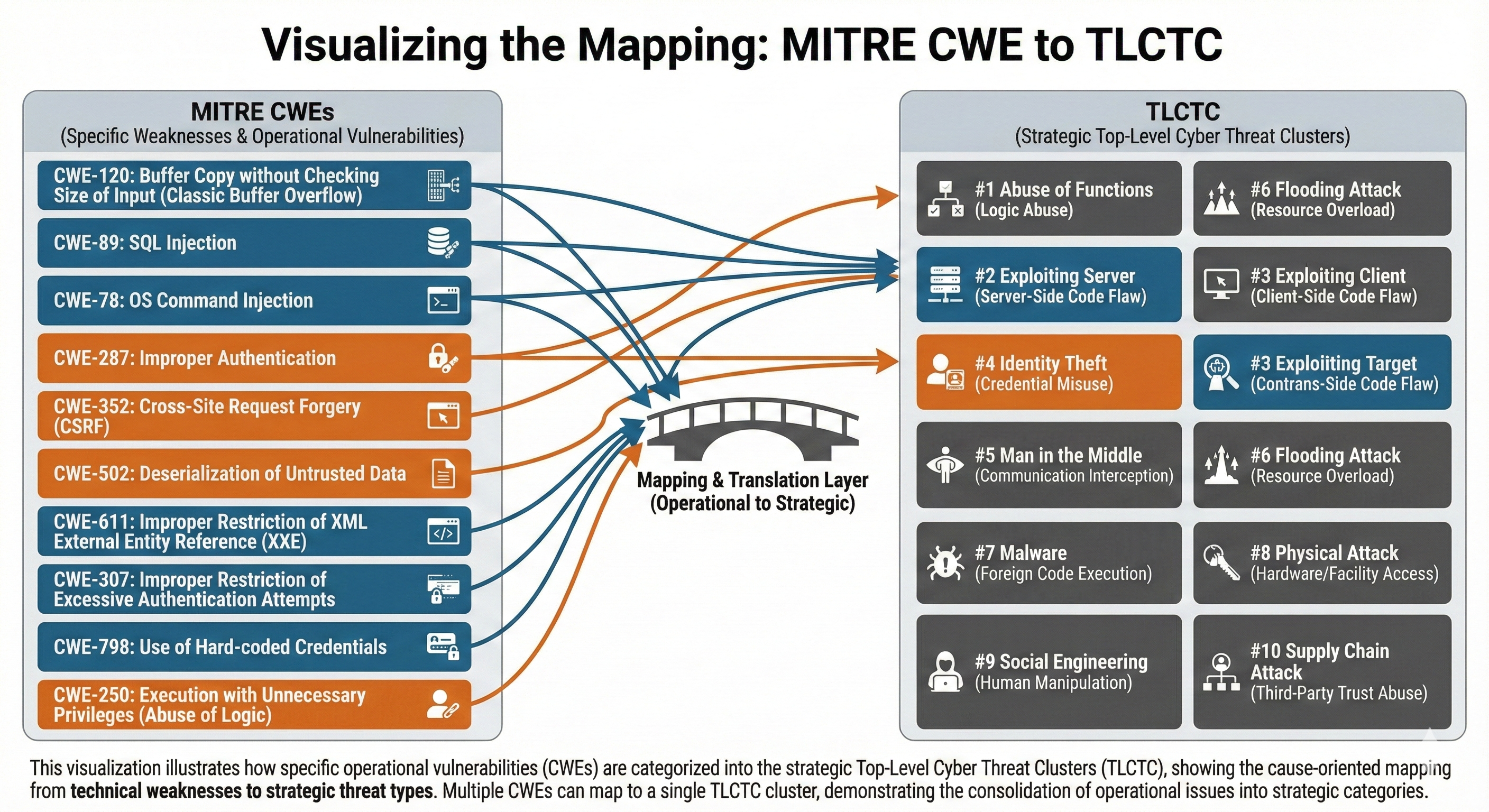
TLCTC & CWE Mapping Explorer
An analysis of the complementary relationship between MITRE CWE and TLCTC. Explains why a 1:1 mapping is not possible and provides an interactive CWE mapping explorer.
ATT&CK Phase Heatmap
Load ATT&CK phase mappings and visualize technique frequency as a heatmap, filtered by TLCTC cluster. Instantly see which clusters dominate each attack phase.
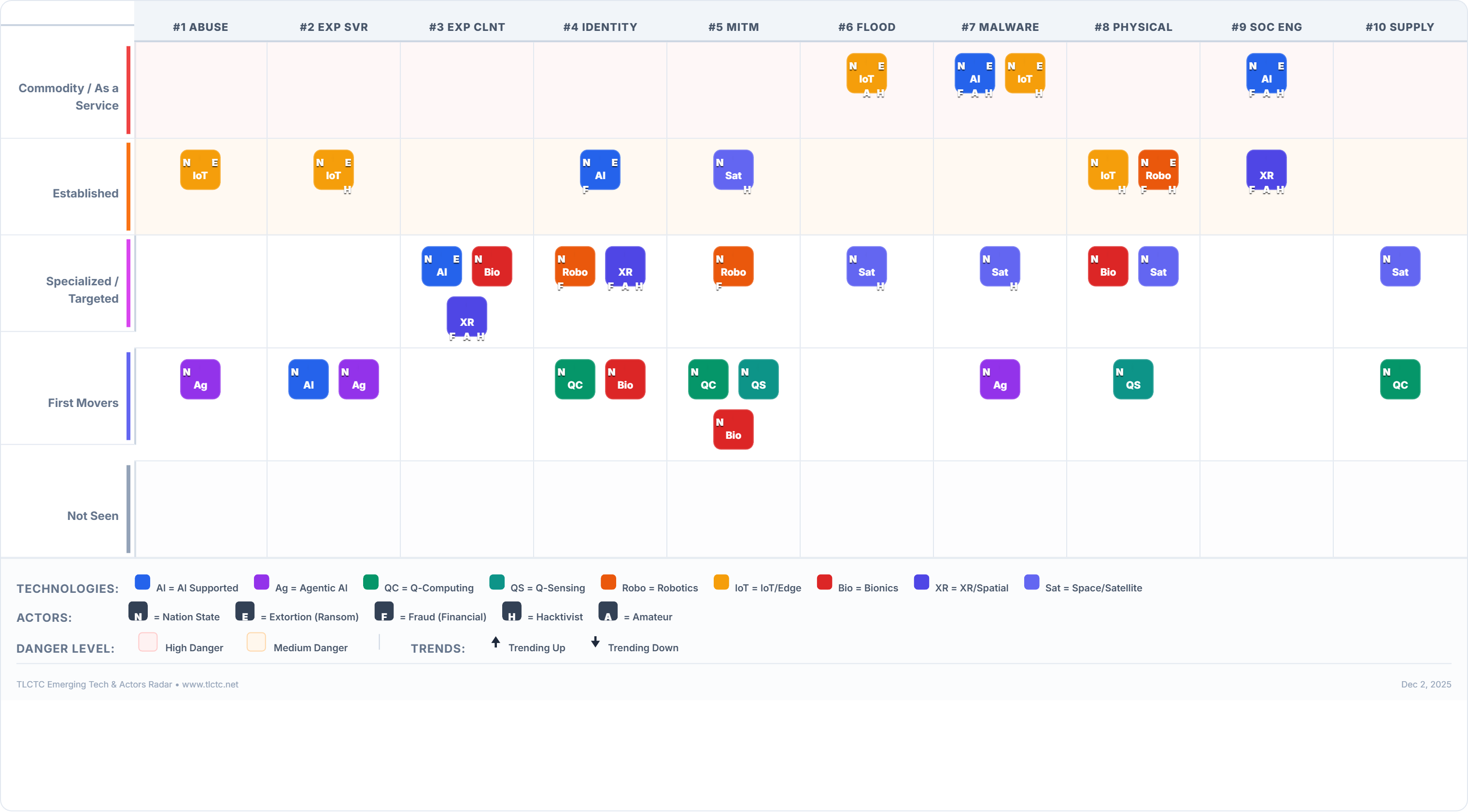
Threat Radar App
Transform dull risk spreadsheets into Board-ready radar visualizations. Map emerging tech and actors directly to the 10 clusters.
See the Threat Capabilities
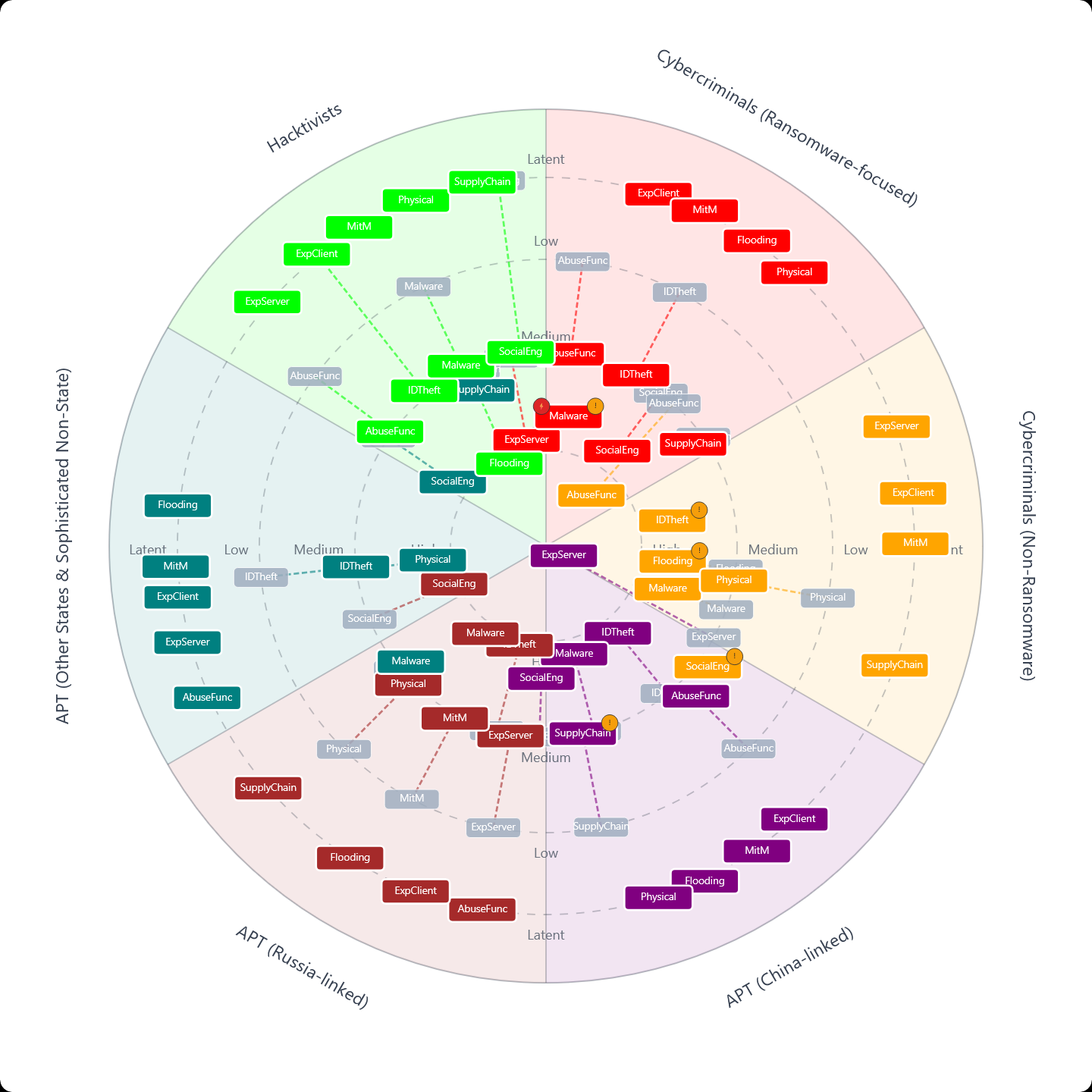
Strategic Threat Profiling: The Actor Profile Designer.
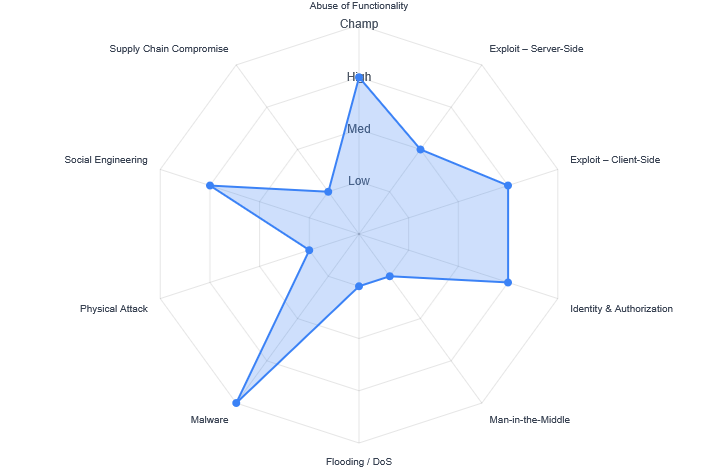
See the Tech Capabilities
Strategic Threat Profiling: The Actor Profile Emerging Tech Radar.

Actor Story Designer
Design threat actor stories combining TLCTC capability profiles and Diamond Model-framed narrative intelligence. Build structured CTI narratives for briefings and exercises.
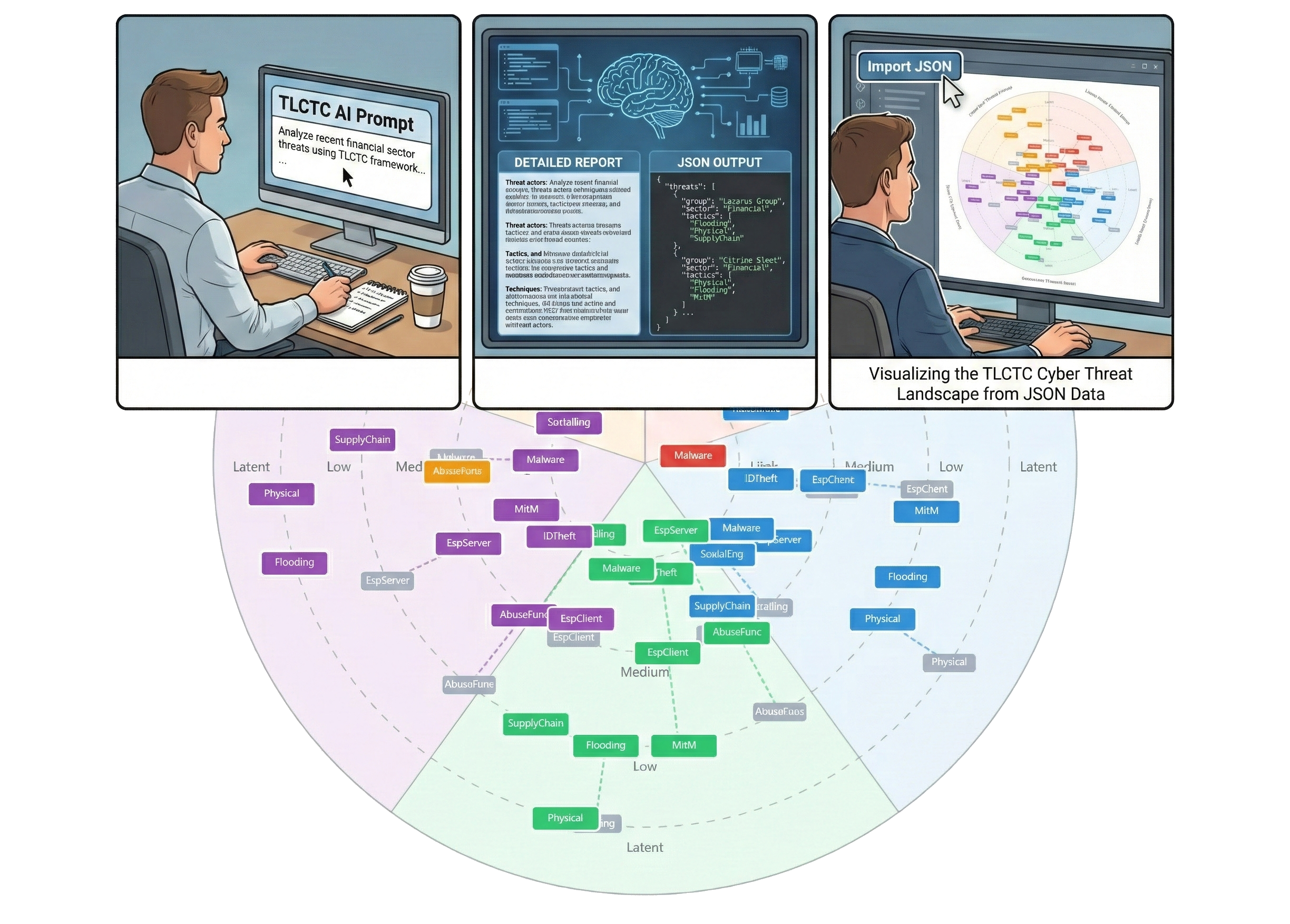
Report to Radar (AI)
Copy-paste prompts to instruct LLMs to parse CTI reports and output valid TLCTC JSON for the Architect and Radar apps.
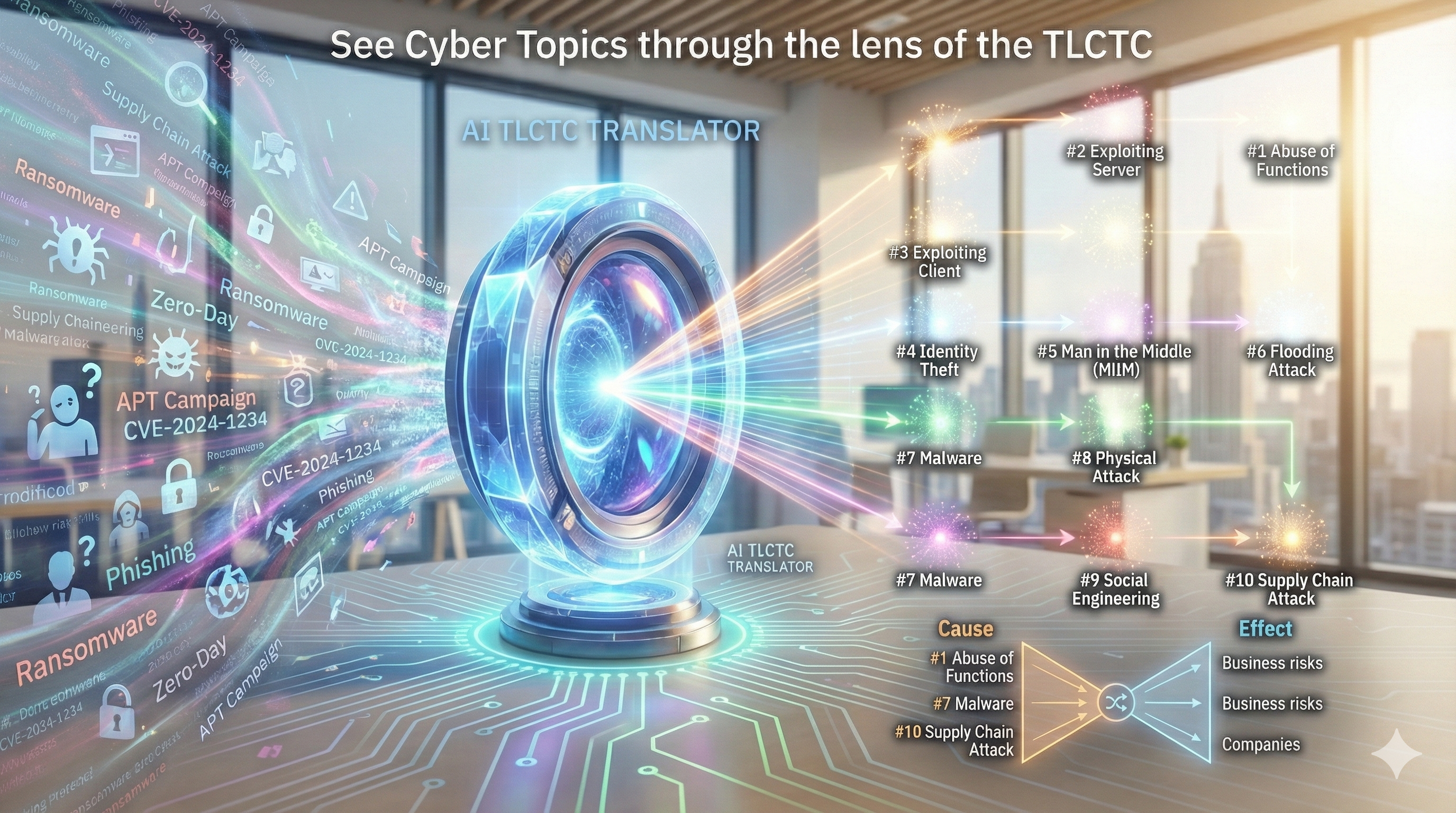
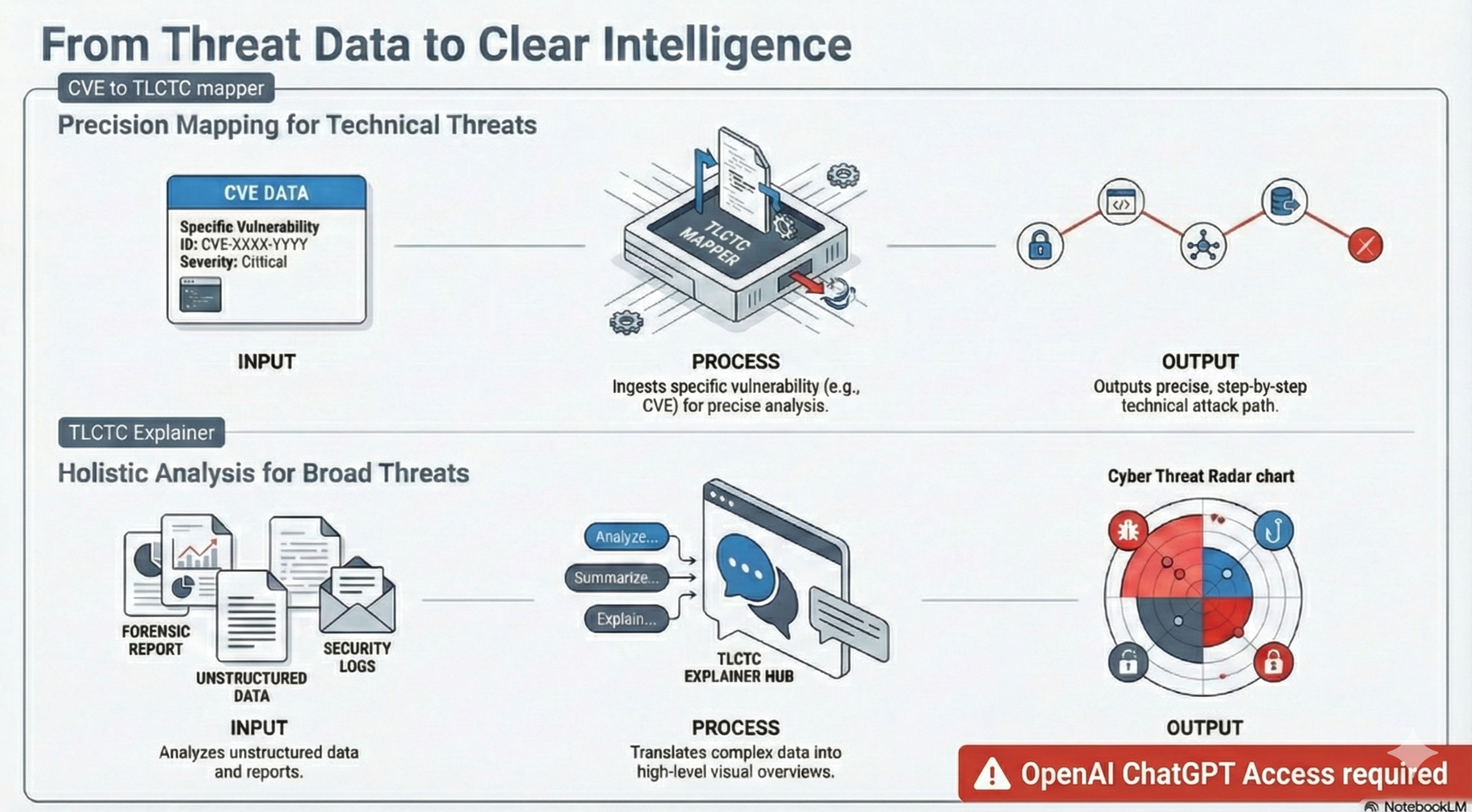
AI Supported Cyber Sec
See Cyber Topics through the lens of the ChatGPT Custom GPT TLCTC Explainer or CVE to TLCTC Mapper. Includes already V2 material.
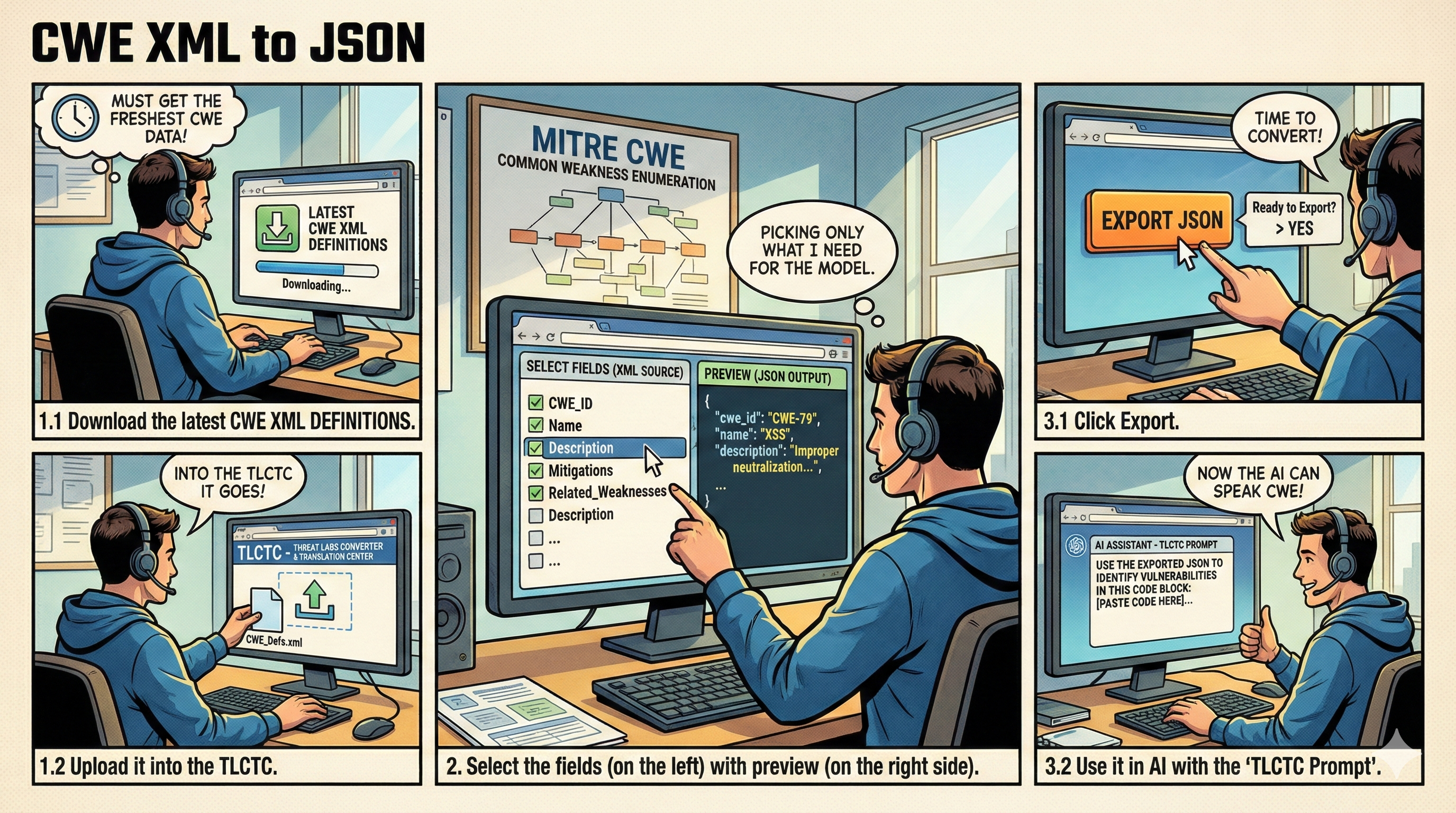
CWE XML Converter
A specialized utility to convert MITRE CWE XML dumps into clean, usable JSON for integration with TLCTC frameworks.
Capability-Based Planning
Map organizational security capabilities across the 10 TLCTC clusters and 6 NIST CSF functions. Assess maturity at the capability level and export structured JSON for governance reporting.
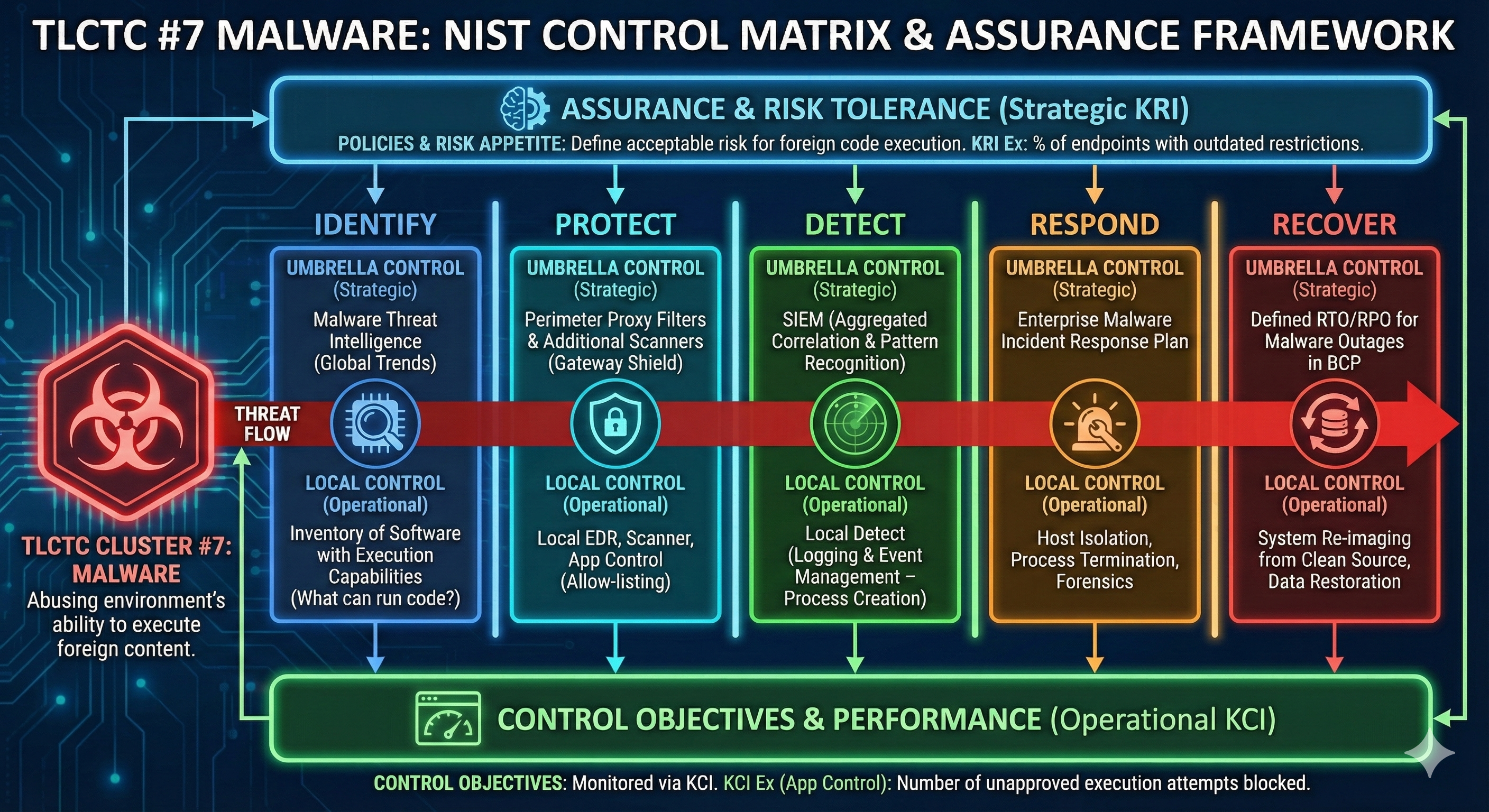
Control Matrix Manager
Manage cyber security control maturity across the 10 TLCTC clusters and 6 NIST CSF functions. Document Local and Umbrella controls per environment and track residual risk.
